I don’t usually write anymore about phishing attempts, but this one draw my attention due to large amount of emails and to variety of websites being used.
Of course, I would not write “massive” if I would have received 1-10, but I receive about 10 a day. Fortunately, almost all go to Spam folder. Gmail is doing a good job!
Let’s have a look:
- Subject:
- is always “Login Details”
- has a prefix, marked with [], usually the name of the website or some slogan of the targeted website.
- Body:
- starts with “Username: the target phishing website, where the user needs to go to reset the password. Looks similar to the one targetted
- a random very large amount of USD, followed by one or more of “BTC pdu diq”.
- Contains a password reset link in the format:
https://[valid domain]/wp-login.php?action=rp&key=[key]&login=[username]. - The username is the phishing website mentioned above
- The structure mimics the real WordPress password reset URLs, using the action=rp parameter and a legitimate reset key, making it seem genuine.
- Domain Mismatch: The reset links use real, but unrelated domains. These are not associated with the recipient in any way.
- The email does not match any WordPress installation the recipient is associated with, which is a critical red flag.
I verified a couple of targeted domains to see if they are compromised, but they did not appear to be so anymore.
This step gives the user the legitimity I guess… But why would a user who has nothing to do with the domain targeted would actually click?
Funny fact:
All those keys have a time to live of probably 24h or less, so by the time they get in an inbox, they are very likely to be expired.
The phishing website:
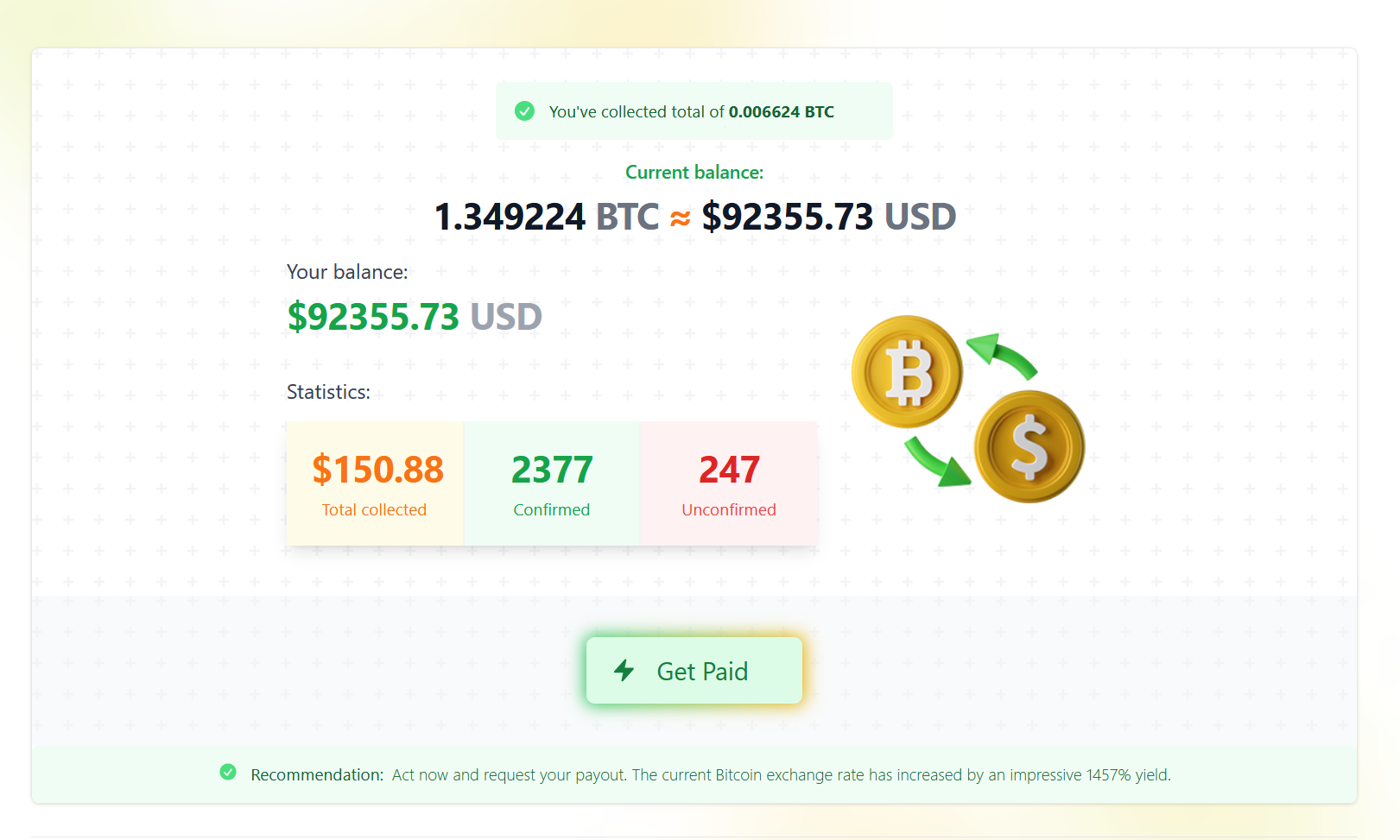
It is always a bitcoin mining account. To convince the user to click, it displays a large amount of money.
Since I was anyway in a sandbox, I said that I have nothing to lose if I continue.
So, the next thing is Figure 2


The final screen is very strange: it shows a continuously increasing counter, and a lot of random numbers.
Looking at the source code, it is indeed random..

I thought that the site is damaged by my sandbox and I forgot about it while writing this article.
After a few minutes, the screen changes and I was asked to “talk” to a payment manager if I want to be paid.
It looks and feels like a bot, because all it does is to ask me for a bank account.
The trick is: If you want the $92K then you must pay a fee of 0.12%.
Final thing… Register to a convertor website to purchase the 64$ into BTC and transfer them to the fraudster.
Conclusion:
I don’t get it.. Who would go through so much trouble to reach this point?
I guess that one must be desperate enough to want the $92K in order to pay the 64$.
© Copyright 2024 Sorin Mustaca, All rights Reserved. Written For: Sorin Mustaca on Cybersecurity
Check www.endpoint-cybersecurity.com for seeing the consulting services we offer.
Visit www.itsecuritynews.info for latest security news in English
Besuchen Sie de.itsecuritynews.info für IT Sicherheits News auf Deutsch









You must be logged in to post a comment.